When evaluating Obot MCP Gateway alternatives, the decision centers on deployment complexity, security compliance, and operational overhead. While Obot provides Kubernetes-native MCP infrastructure, many enterprises seek platforms offering faster deployment, comprehensive governance, or simplified authentication without infrastructure complexity.
This comprehensive guide examines the top Obot alternatives, with particular emphasis on why MintMCP's MCP Gateway is a strong option for production deployments.
Key takeaways
- MintMCP Gateway is a strong Obot alternative for enterprise deployments with managed SaaS-first deployment, SOC 2 Type II attestation, SSO and SCIM-driven RBAC, and OAuth brokering for stdio and hosted MCP servers
- Obot requires Kubernetes expertise with Kubernetes-oriented production deployment and quick Docker pilots, versus MintMCP's managed SaaS-first deployment
- Security compliance varies dramatically: MintMCP is SOC 2 Type II audited, compliant with HIPAA standards, provides complete audit trails, while open-source options place certification and control implementation on the customer
- Build vs. buy economics favor commercial platforms: high-six-figure initial builds are common; annual maintenance often runs 15–25% of initial cost and can be higher for complex systems
- Enterprise MCP adoption centers on governance: Centralized authentication, complete observability, tool-level policy, credential management, and policy enforcement separate production-ready platforms from developer tools
- Choose based on deployment priorities: Select MintMCP for rapid enterprise deployment and centralized governance, Obot for Kubernetes-native control, open-source alternatives for maximum customization
Understanding Obot MCP gateway: Kubernetes-native infrastructure
Obot positions itself as a Kubernetes-native MCP gateway designed for teams with existing container orchestration expertise. The platform emphasizes cloud-native deployment patterns and infrastructure-as-code approaches familiar to DevOps engineers.
Key Obot strengths:
- Kubernetes-native architecture for teams with existing cluster infrastructure
- Container-based deployment model with resource isolation
- Open-source foundation enabling customization and code access
- Infrastructure-as-code compatibility for GitOps workflows
- Session-aware routing for multi-step AI workflows
Significant limitations:
- Kubernetes-oriented production deployment with quick Docker pilots available
- Self-managed compliance evidence and control implementation requiring additional audit preparation
- Kubernetes expertise is required for production deployment and ongoing operations
- Self-managed infrastructure overhead demands ongoing operational resources
- Limited centralized governance without additional policy, identity, and observability tooling
The platform appeals to technically sophisticated teams prioritizing infrastructure control over deployment speed. However, the operational complexity and manual security configuration create friction for enterprises seeking rapid production deployment with built-in governance.
1. MintMCP gateway: Enterprise-grade alternative
MintMCP Gateway transforms MCP from developer utility to production-ready infrastructure with enterprise security, managed SaaS-first deployment, and comprehensive governance without requiring Kubernetes expertise.
Key MintMCP advantages:
- SOC 2 Type II audited
- Compliant with HIPAA standards
- Managed SaaS-first deployment in the US and EU, with VPC/self-hosted deployment on request
- SSO and SCIM-driven RBAC for centralized identity and access control
- Tool-level allowlisting and rule-based policy for granular governance
- Virtual MCP Bundles providing per-use-case endpoints with SCIM-driven membership
- Agent Bundles with M2M auth and “act as agent” flow
- OAuth brokering for stdio and hosted MCP servers
- Complete audit trails tracking every tool call, access request, and configuration change
- Centralized observability with live dashboards for usage and security review
- Hosted MCP connectors run by MintMCP so teams do not need to manage connector runtimes, scaling, or Kubernetes pods
Enterprise security and compliance
MintMCP Gateway addresses the authentication complexity plaguing MCP adoption with OAuth brokering, SSO, and SCIM-driven RBAC. The platform provides:
- Enterprise SSO enforcement with OIDC and SAML support
- SCIM-driven RBAC using IdP groups for access control
- Granular access control with tool-level allowlisting and rule-based policy
- SOC 2 Type II audited
- Compliant with HIPAA standards
- Shared and per-user auth supporting both service accounts and individual OAuth flows
- Credential management for governed MCP access across teams and agents
Deployment speed and simplicity
Unlike Obot's Kubernetes requirements, MintMCP enables production deployment without infrastructure overhead. The platform hosts MCP connectors on MintMCP infrastructure, making containerized servers accessible without local installations. Virtual MCP Bundles, pre-configured policies, and self-service access requests eliminate the weeks-long setup traditional platforms demand.
Comprehensive observability
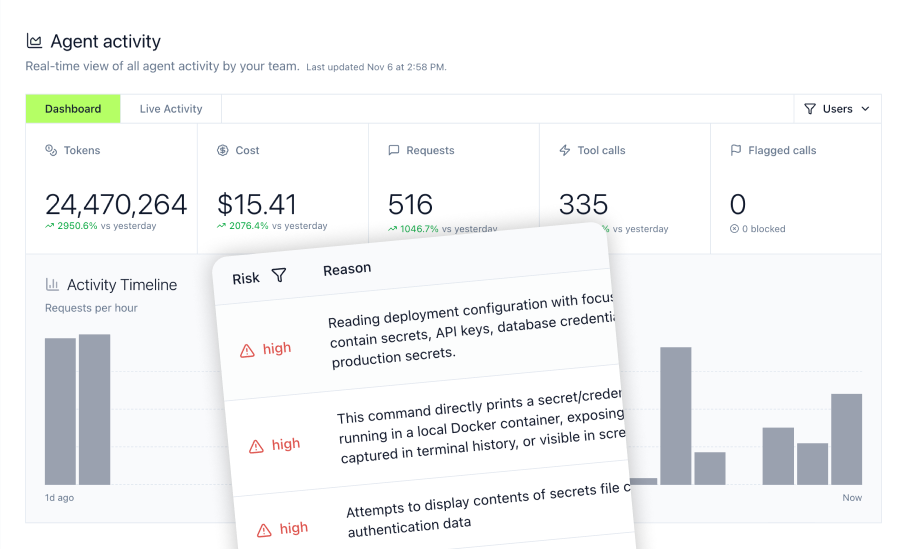
MintMCP’s Gateway and Agent Monitor provide visibility beyond traditional API gateways:
- Track every MCP tool invocation, including tool access patterns and policy decisions
- Monitor installed MCPs across Claude, Cursor, ChatGPT, Gemini, Copilot, and other agents with usage analytics
- Block dangerous commands in real-time, protecting sensitive files
- Complete command history with audit trails for security review
- Cost analytics tracking spending per team, project, and tool
Integration ecosystem
MintMCP's connector library enables rapid AI agent deployment across business functions:
- Elasticsearch MCP Server for knowledge base search and log analysis
- Snowflake MCP Server for financial reporting and data analytics
- Gmail MCP Server for customer support automation
Pricing structure
Contact MintMCP for enterprise pricing customized to deployment scale and compliance requirements. The platform's value proposition centers on eliminating the hundreds of thousands of initial investment required for internal gateway development.
2. Docker MCP gateway
Docker's MCP Gateway implementation leverages familiar containerization patterns for teams already using Docker infrastructure. The platform provides cryptographically signed images with resource isolation.
Docker Gateway Strengths:
- Container-native deployment is familiar to teams using Docker
- Resource isolation runs servers in isolated containers with restricted CPU/memory/network as configured
- Cryptographically signed images for supply chain security
- Open-source foundation enabling code inspection and customization
- Simpler than Kubernetes for teams without orchestration expertise
Limitations to Consider:
- Manual security configuration gateway provides security features such as OAuth support, signature verification, and call logging; enterprise SSO/IdP integration varies by setup
- Self-managed compliance evidence and control implementation requiring additional audit preparation
- Self-managed infrastructure demanding operational overhead
- Built-in logging/call-tracing, with deeper monitoring layered on separately
- Scalability and high availability may require extra operations work for production deployments
- No MintMCP-style Virtual MCP Bundles or Agent Bundles for per-use-case endpoints, SCIM-driven membership, per-agent identity, and M2M auth
Docker MCP Gateway appeals to developer-focused teams prioritizing container familiarity over managed governance features.
3. IBM ContextForge
IBM ContextForge emphasizes session-aware routing and enterprise integration patterns, targeting organizations with existing IBM infrastructure investments.
ContextForge features:
- Session-aware routing for complex multi-step workflows
- Enterprise integration patterns familiar to IBM customers
- Open-source foundation under Apache 2.0
- Advanced workflow capabilities for sophisticated business logic
- IBM ecosystem integration for teams already standardized on IBM infrastructure
Deployment considerations:
- Quick start via PyPI/Docker; K8s for scale/federation
- Built-in auth with user-scoped OAuth tokens; SSO configuration available
- Self-managed infrastructure requiring operational resources
- Learning curve for teams unfamiliar with IBM patterns
- Additional governance work may be needed for SCIM-driven RBAC, per-use-case tool bundles, agent identity, and centralized MCP observability
IBM ContextForge appeals primarily to existing IBM customers seeking MCP gateway capabilities within their current infrastructure.
4. TrueFoundry
TrueFoundry extends its MLOps platform to support MCP gateway functionality, offering AI infrastructure for teams managing both model deployment and MCP servers.
TrueFoundry platform capabilities:
- Unified AI infrastructure managing LLMs and MCP servers
- MLOps workflow support for teams managing model deployment and agent workflows
- Deployment support for RAG and agent workflows
- Multi-model proxying for LLM infrastructure
- Container-first architecture for modern deployments
- Hybrid deployment with managed SaaS and self-hosted control plane options
Platform limitations:
- Implementation timelines vary with scope; larger MLOps rollouts can be non-trivial
- MLOps complexity exceeding the needs for MCP-only deployments
- Higher pricing tiers compared to purpose-built MCP solutions
- Steep learning curve for teams without an MLOps background
- Infrastructure overhead requiring dedicated DevOps resources
- MCP governance depth should be evaluated for Virtual MCP Bundles, Agent Bundles, tool-update policy, and centralized employee-agent governance
TrueFoundry serves teams requiring comprehensive MLOps capabilities beyond MCP gateway functionality, though simpler alternatives exist for MCP-focused deployments.
5. API gateway extensions
Traditional API gateway platforms extend their capabilities to support MCP, appealing to organizations seeking unified traffic management across APIs and AI workflows.
API gateway approach:
- Existing infrastructure leverage for teams using Kong, Tyk, or similar platforms
- Unified traffic management combining API and MCP governance
- Familiar patterns for teams experienced with API gateways
- Mature monitoring capabilities from established platforms
MCP-specific challenges:
- Limited MCP-native features compared to purpose-built solutions
- Manual MCP configuration, adapting API gateway patterns
- Incomplete governance for AI-specific requirements
- Authentication complexity mapping OAuth to MCP servers
- Observability gaps for AI agent behavior tracking
- Missing MCP-specific primitives may include Virtual MCP Bundles, Agent Bundles, tool-update policy, stdio/hosted-server OAuth brokering, and Gateway + Agent Monitor two-layer governance
These platforms suit organizations prioritizing unified infrastructure over MCP-optimized features, though purpose-built solutions provide stronger AI-specific governance capabilities.
Enterprise use cases: Which alternative fits your needs
Financial services and regulated industries
Organizations in finance, healthcare, and other regulated sectors require comprehensive governance:
Choose MintMCP Gateway for:
- Complete audit trails tracking every tool call and access request
- Tool-level allowlisting and rule-based policy for governed access
- Automated policy enforcement reduces manual compliance tasks
- Snowflake integration for financial reporting and analytics
Financial services deployments demand the compliance support and governance capabilities that manual platforms require extensive custom development to achieve.
Developer-Centric organizations with Kubernetes expertise
Teams with deep Kubernetes knowledge and existing cluster infrastructure may prioritize infrastructure control:
Select Kubernetes-native alternatives when:
- Existing Kubernetes expertise reduces cluster setup overhead; timelines vary by org and environment
- Infrastructure-as-code workflows require GitOps integration
- Maximum customization outweighs deployment speed
- Internal resources available for ongoing maintenance
- Open-source foundation enables code inspection
However, even Kubernetes-savvy teams increasingly evaluate managed solutions to reduce operational overhead and focus engineering resources on core product development.
Rapid MVP development and market validation
Startups and product teams requiring fast deployment for market validation prioritize speed over infrastructure control:
MintMCP Gateway excels in:
- Managed SaaS-first deployment with faster setup than DIY/K8s paths
- Hosted MCP connectors run by MintMCP
- Pre-configured policies enabling faster production deployment
- Self-service access reduces approval friction
- Complete observability from day one without additional tooling
MintMCP’s managed deployment model can prove critical for teams validating AI agent workflows quickly.
Enterprise AI infrastructure consolidation
Organizations deploying multiple AI tools, including ChatGPT, Claude, Cursor, Gemini, Copilot, and custom agents across teams, require unified governance:
Unified platform benefits:
- Centralized authentication eliminates per-tool security implementations
- Complete audit trails across all AI agents and MCP servers
- Cost attribution tracking spending per team and project
- Policy enforcement applying consistent governance rules
- Real-time monitoring detects anomalies across tools
- Virtual MCP Bundles and Agent Bundles govern per-use-case access and per-agent identity
The Gateway + Agent Monitor model provides visibility that traditional API gateways lack, tracking tool calls, bash commands, and file access across coding agents.
Build vs. Buy: The total cost calculation
Internal development costs
Building an MCP gateway internally requires substantial investment:
- Often six-figure initial builds, ongoing maintenance commonly 15–25% and higher for regulated or complex environments
- Ongoing maintenance for updates, security reviews, and compliance evidence
- Continuous resource allocation for MCP spec compliance as protocol evolves
- Security implementation requiring specialized expertise
- Opportunity cost of engineering resources diverted from the core product
Commercial platform economics
Managed MCP gateway platforms provide predictable costs:
- Enterprise pricing varies by scale and features; request a quote
- Continuous MCP spec updates reduce the ongoing development burden
- Dedicated support versus internal troubleshooting
- Faster time to value, enabling teams to deploy governed AI workflows sooner
Hidden costs of Open-Source alternatives
Open-source MCP gateways carry operational overhead:
- Ongoing maintenance for security patches and updates
- Compliance implementation requires additional tooling and audits
- Training overhead for team onboarding and expertise development
- Monitoring solutions are purchased separately for observability
- Support limitations relying on community versus dedicated assistance
The build vs. buy calculation increasingly favors commercial platforms as enterprises recognize the total cost of ownership extends far beyond initial development.
Security and authentication: Critical differentiators
Enterprise authentication requirements
MCP adoption initially struggled with authentication complexity, lacking standardized mechanisms for enterprise security. Modern gateways address this through varying approaches:
MintMCP's OAuth Brokering and Identity Controls:
- OAuth brokering for stdio and hosted MCP servers
- SAML and OIDC integration with enterprise identity providers
- SCIM-driven RBAC using IdP groups
- Shared and per-user authentication supporting both service accounts and individual flows
- Tool-level allowlisting and rule-based policy for sensitive operations
- Complete audit trails tracking authentication and access events
Manual Implementation Alternatives:
- Open-source gateways often require configuring IdP/SSO; many OSS gateways include OAuth support out of the box.
- Kubernetes-native solutions demand identity provider configuration
- API gateway extensions need MCP-specific authentication mapping
- Self-managed platforms create an ongoing security maintenance burden
Compliance and audit trail requirements
Regulated industries require comprehensive audit capabilities:
MintMCP Compliance Features:
- **SOC 2 Type II **audited
- Compliant with HIPAA standards
- **Complete audit trails **tracking tool calls, access requests, and configuration changes
- Automated policy enforcement reduces manual compliance tasks
Alternative Approaches:
- Open-source solutions require OSS gateways to provide logging/OTel; formal compliance reporting remains your responsibility
- Manual compliance preparation extends deployment timelines
- Custom development needed for regulatory reporting
- Ongoing audit maintenance creates operational overhead
Real-Time security controls
AI agent unpredictability demands active security monitoring:
Agent Monitor Security Capabilities:
- Block dangerous commands before execution, protecting sensitive systems
- Sensitive file protection preventing access to .env files, SSH keys, credentials
- Real-time monitoring detects anomalous agent behavior
- Complete command history for security investigation and forensics
- Tool governance controls which MCP tools agents can access
Traditional API gateways lack the AI-specific security controls production agent deployments require.
Observability and monitoring: Operational visibility
AI Agent-Specific monitoring challenges
AI agents create unpredictable traffic patterns unlike human-driven applications:
- Hundreds of tool calls from single-agent sessions
- Traffic bursts from agent retry loops
- Cost spikes from inefficient prompt patterns
- Security events from tool-based prompt injections
- File access patterns requiring granular tracking
Traditional API gateway metrics fail to distinguish productive automation from agents stuck in loops or cost-driving operations.
Comprehensive MintMCP observability
The MCP Gateway provides real-time visibility:
- Usage analytics track every tool call and MCP server interaction
- Cost attribution mapping spending to teams, projects, and agents
- Performance metrics measuring response times and error rates
- Security dashboards detecting anomalies with configurable alerting
- Compliance reporting generates audit trails for regulatory requirements
The Agent Monitor extends monitoring to coding agents:
- Track installed MCPs across Claude, Cursor, ChatGPT, Gemini, Copilot, and other agents
- Monitor file access to sensitive data and configuration
- Bash command history with complete audit trails
- Block risky operations in real-time before execution
Alternative monitoring approaches
Open-source and API gateway alternatives require separate observability tooling:
- API observability tools for deeper traffic monitoring
- Custom Prometheus/Grafana dashboards for metrics
- Separate logging solutions for audit trail management
- Manual cost attribution tracking spending across teams
- Additional monitoring costs beyond gateway platform fees
Making the right choice for your organization
When to choose MintMCP gateway
MintMCP Gateway excels for organizations prioritizing:
- Rapid deployment requiring production capability without weeks of Kubernetes setup
- Enterprise compliance support
- Simplified operations, eliminating Kubernetes infrastructure overhead
- Complete governance with OAuth brokering, centralized authentication, and SCIM-driven RBAC
- Comprehensive observability tracking tool calls, costs, and security events
- Agent governance with Virtual MCP Bundles, Agent Bundles, and Gateway + Agent Monitor coverage
When to consider alternatives
Kubernetes-native solutions suit teams where:
- Deep Kubernetes expertise eliminates infrastructure setup complexity
- Maximum infrastructure control outweighs deployment speed
- GitOps workflows require infrastructure-as-code integration
- Internal development resources are available for ongoing maintenance
- Open-source foundation critical for code inspection requirements
API gateway extensions fit organizations where:
- Existing Kong, Tyk, or similar infrastructure seeks unified management
- API and MCP traffic consolidation provides operational efficiency
- Familiar patterns outweigh MCP-optimized features
- Current monitoring capabilities extend to MCP workloads
Frequently asked questions
What is the difference between an MCP gateway and a traditional API gateway?
MCP gateways provide AI-specific capabilities beyond traditional API management: session-aware routing for multi-step workflows, AI agent behavior monitoring, tool governance, and cost attribution tracking of unpredictable agent patterns. Traditional API gateways handle request routing and authentication, but lack the observability needed to distinguish productive automation from agents stuck in loops or security threats from tool-based prompt injections.
Do I need a separate MCP gateway if I already use AWS API gateway or Azure APIM?
Yes, for production AI agent deployments. While AWS and Azure provide basic proxying, they lack MCP-native features like OAuth brokering for stdio and hosted MCP servers, complete audit trails for compliance, AI agent-specific monitoring, and tool governance capabilities. The MCP Gateway provides purpose-built infrastructure versus adapting a general API management.
Can I deploy an MCP gateway on-premises for data residency requirements?
MintMCP Gateway is managed SaaS-first in the US and EU, with VPC/self-hosted deployment available on request. Kubernetes-native alternatives such as Obot and IBM ContextForge support self-hosted deployment but require infrastructure setup and ongoing operational overhead versus managed solutions.
How does middleware differ from an MCP gateway in AI infrastructure?
Middleware focuses on message transformation, protocol translation, and service composition, while MCP gateways provide centralized governance for AI agent tool access. MCP gateways include authentication enforcement, audit trail generation, real-time security controls, and AI-specific monitoring that middleware platforms lack. Some organizations use both: middleware for data transformation and MCP gateways for agent governance.
What is the typical deployment timeline for a managed MCP gateway vs. Building custom infrastructure?
MintMCP Gateway enables faster production deployment through managed infrastructure and pre-configured policies. Kubernetes-native alternatives can require days or weeks for cluster setup and configuration, depending on the environment. Custom development demands significant initial investment and ongoing maintenance, making managed platforms attractive for teams prioritizing speed and eliminating operational burden.