When evaluating Lasso.Security MCP Gateway alternatives, the decision ultimately depends on your deployment speed requirements, security compliance needs, and enterprise infrastructure complexity. While Lasso.Security emphasizes security-first architecture with plugin-based guardrail systems, many engineering leaders seek platforms offering faster deployment timelines, broader AI agent compatibility, or more complete governance for authentication, access control, credential management, logging, and agent oversight.
This guide examines the top Lasso.Security alternatives, with particular emphasis on why the MintMCP Gateway is a strong choice for enterprise MCP deployment.
Key takeaways
- MintMCP Gateway stands out as a strong alternative for enterprise MCP infrastructure with fast managed deployment, SOC 2 Type II attestation, HIPAA Compliant (BAA Available) support, and native governance for Claude, ChatGPT, Cursor, Gemini, Copilot, and other MCP-compatible clients
- Lasso.Security focuses on security depth with built-in secret detection and guardrail patterns, but teams should also evaluate whether they need SCIM-driven RBAC, per-use-case tool bundles, audit logs, credential management, and agent identity governance
- Deployment models vary dramatically: MintMCP is managed SaaS-first with US and EU availability plus VPC/self-hosted options on request, Docker MCP Gateway is container-native, and TrueFoundry is a broader hybrid MLOps control plane
- Learning curves impact time-to-value: purpose-built MCP gateways can shorten deployment and governance setup compared with broader platforms that require Kubernetes, MLOps, or custom gateway engineering expertise
- Security compliance is non-negotiable: Choose platforms that provide SOC 2 Type II attestation, HIPAA Compliant (BAA Available) support where required, centralized audit trails, and policy enforcement across users, agents, tools, and connectors
What is an MCP gateway, and why enterprise teams need one
The Model Context Protocol (MCP) ecosystem expanded following Anthropic's November 2024 release, creating critical infrastructure gaps between protocol specification and production-ready deployment. While MCP solved integration challenges between AI agents and external tools, it introduced new security, observability, and operational management requirements that the base protocol doesn't address.
MCP Gateways function as centralized orchestration and governance layers, essentially reverse proxies and control planes sitting between AI agents and multiple MCP servers. These gateways provide:
Core gateway capabilities:
- Unified endpoint principle: Single gateway connection versus managing multiple server connections
- Separation of concerns: Offloading security and routing from individual tool servers
- Policy enforcement: Centralized security policies applied consistently across all backends
- Session-aware proxying: Request routing with comprehensive observability and audit trails
Enterprise challenges MCP gateways solve
The integration chaos problem becomes exponential as the MCP server count grows. Each server maintains an independent authentication state, session management, authorization policies, and security event logging. Without gateways, organizations face:
- Security fragmentation: Individual OAuth setups per server create multiple failure points and inconsistent security postures
- Visibility black holes: Direct MCP connections provide zero insight into agent actions, tool usage, and data access patterns
- Configuration sprawl: Synchronizing server configurations across environments becomes unmanageable at scale
- Compliance gaps: Implementing organization-wide security policies across fragmented systems proves nearly impossible
The MCP gateway market addresses these production gaps through infrastructure that transforms local MCP servers into governed services with monitoring, logging, and compliance support.
1. MintMCP gateway: Enterprise MCP infrastructure with fast managed deployment
MintMCP Gateway helps enterprise teams deploy MCP infrastructure by combining production-focused security with rapid managed setup. MintMCP is managed SaaS-first with US and EU availability, with VPC/self-hosted deployment available on request. As a platform with SOC 2 Type II attestation, HIPAA Compliant (BAA Available) support, and hosted MCP connector capabilities, MintMCP addresses the gap between basic open-source implementations and complex MLOps platforms.
Key MintMCP advantages:
- Hosted MCP connectors: Run hosted MCP connectors on MintMCP infrastructure with managed lifecycle support
- OAuth brokering for stdio and hosted MCP servers: Enterprise authentication wrapping for MCP endpoints without requiring each team to build custom OAuth flows
- SOC 2 Type II attestation: Compliance support with centralized audit trails, plus HIPAA Compliant (BAA Available) support
- Virtual MCP Bundles: Per-use-case endpoints with SCIM-driven membership, curated tool sets, and granular access policies per team or agent
- Real-time monitoring dashboards: Live visibility into server health, usage patterns, and security alerts
- Complete audit trails: Logging of tool calls, authentication events, and configuration changes
- Agent Bundles: Per-agent identity with M2M auth and “act as agent” flow for agent-specific governance
Enterprise security features
MintMCP implements centralized governance with OAuth 2.0, SAML, SSO, SCIM-driven RBAC, credential management, and tool-level policy. The platform's granular tool access control enables configuration by role, restricting write operations while enabling read-only access for specific teams.
AI client compatibility
Unlike security-focused platforms supporting limited clients, MintMCP provides governance for:
- Claude Desktop and Claude Code
- ChatGPT via Custom GPTs
- Cursor IDE
- Microsoft Copilot
- Gemini, Goose, Windsurf
- LibreChat and Open WebUI
- Custom MCP-compatible agents
MCP connector ecosystem
MintMCP's central registry provides installation for enterprise integrations:
- Elasticsearch MCP Server: Enterprise search with query DSL, ES|QL, and semantic capabilities for HR, product, and support teams
- Snowflake MCP Server: Natural language to SQL via Cortex Analyst with semantic models for finance and analytics teams
- Gmail MCP Server: Secure email automation with threading integrity and access controls for customer support workflows
Deployment speed
The infrastructure gap between protocol specification and production-ready deployment proved larger than anticipated. MintMCP addresses this through managed SaaS-first deployment, hosted MCP connectors, OAuth brokering for stdio and hosted servers, and policy primitives such as Virtual MCP Bundles.
Pricing structure
MintMCP offers enterprise pricing through consultation. Contact enterprise@mintmcp.com for deployment planning.
Real-World applications
Organizations leverage MintMCP Gateway for:
- Database analysis: AI agents querying PostgreSQL, MySQL, and Snowflake with governed access
- Customer support: Assistants accessing CRM data and support tickets through Gmail integration
- Development workflows: Connecting coding assistants to repositories and CI/CD via Cursor and VS Code
2. TrueFoundry
TrueFoundry positions itself as a comprehensive AI infrastructure control plane for model deployment orchestration. The platform includes MCP gateway capabilities as part of broader MLOps management.
TrueFoundry strengths:
- Performance optimization: Low-latency internal routing, with best-case latency claims depending on deployment configuration
- Unified LLM + MCP management: Consolidated vendor relationship for comprehensive AI infrastructure
- GPU utilization improvements: Optimized model deployment infrastructure
- RAG/Agent deployment support: Acceleration versus traditional ML platforms
Implementation challenges:
- Over-engineering risk: Comprehensive MLOps features are unnecessary for teams focused solely on MCP deployment
- Operational complexity: Broader AI infrastructure platforms may require Kubernetes, model deployment, and ML platform expertise beyond MCP gateway administration
- Governance fit: Teams should evaluate whether the platform provides MCP-specific primitives such as per-use-case tool bundles, SCIM-driven membership, tool-update policy, and per-agent identity governance
Ideal use cases
Organizations requiring unified model deployment, training orchestration, and MCP gateway functionality in a single platform, and willing to invest setup time for consolidated infrastructure.
3. IBM ContextForge
Open-source implementations like IBM ContextForge and LiteLLM MCP offer zero licensing costs with full customization capabilities for teams with development resources.
Open-Source platform benefits:
- No licensing costs: Free deployment with unrestricted usage
- Full customization: Complete code access for specific enterprise requirements
- Community support: Active developer communities for troubleshooting and feature requests
- Vendor independence: No lock-in concerns with self-managed infrastructure
Operational requirements:
- Development resources: Manual security implementation and compliance infrastructure
- Self-managed compliance: Organizations must build audit, logging, policy, and identity infrastructure independently
- Support model evaluation: Open-source projects typically require internal ownership for production operations unless a commercial or third-party support option is verified
- Governance gap: Teams should assess whether self-managed options provide SCIM-driven RBAC, Virtual MCP Bundles, Agent Bundles, credential management, hosted connector operations, and centralized audit trails out of the box
When to consider
Teams with significant development capacity prioritizing customization over managed services, or organizations with existing security infrastructure seeking MCP-specific extensions. However, many enterprises prefer managed services with SLAs over DIY approaches requiring internal expertise.
4. Docker MCP gateway
Docker MCP Gateway treats MCP servers as containerized workloads with isolation controls. This approach appeals to container-experienced teams.
Container-Native advantages:
- Familiar security models: Docker-based isolation patterns for operations teams
- Sandboxed execution: Containerized execution with configurable resource and filesystem controls
- Container ecosystem integration: Works with existing Docker orchestration tools
Performance trade-offs:
- Latency and operations overhead: Container isolation and orchestration can add operational considerations versus managed gateway implementations
- Docker expertise required: Effective deployment demands container management skills
- Policy ownership: Teams remain responsible for defining and operating least-privilege policies, identity integration, connector lifecycle, and audit workflows
Tradeoffs to consider
Docker's container-native model can fit teams that already operate container infrastructure, but it may make centralized MCP governance harder if teams also need SCIM-driven RBAC, Virtual MCP Bundles, OAuth brokering for stdio and hosted servers, managed connector runtime, and agent-specific identity governance. MintMCP addresses these needs through managed SaaS-first deployment and gateway-native policy primitives.
5. Kong AI gateway
Kong AI Gateway does not provide native MCP gateway capabilities, but it offers a highly extensible API management foundation that teams can use to build their own MCP gateway layer. Organizations already operating Kong for service governance can implement custom plugins and routing logic to translate MCP traffic, enforce policies, and manage multi-server architectures.
Kong platform strengths:
- Plugin ecosystem: Authentication, rate limiting, traffic shaping, and observability capabilities that can be repurposed for MCP control planes
- Extensible architecture: Custom plugins allow teams to implement MCP-specific behaviors such as session handling, tool-call routing, and audit logging
- API management: Support for large deployments, with Kong Mesh and Konnect providing multi-cluster and multi-region operating models
- AI-aware routing capabilities: Semantic routing and intelligent caching can complement MCP workflows when building a unified AI services gateway
Limitations and considerations:
- Not MCP-native: Teams must build MCP session management, transport adapters, and protocol envelopes themselves
- Engineering investment required: Developing a full MCP proxy layer on top of Kong demands significant platform engineering resources and internal expertise
- Feature overhead: Kong’s broad API feature set is often more than what MCP-focused deployments require, increasing operational surface area
- Governance primitives: Teams should evaluate whether custom Kong implementations can provide MCP-specific features such as Virtual MCP Bundles, Agent Bundles, tool-update policy, OAuth brokering for stdio and hosted MCP servers, and centralized agent audit trails
Cost considerations:
- Pricing complexity: Enterprise API gateway pricing can scale by services, requests, runtimes, or deployment footprint. Cost modeling can become complex as workloads grow
- Budget unpredictability: Usage-based billing can create variable monthly costs, especially for AI-driven, bursty, or agent-heavy workloads
- Custom development cost: Building MCP-specific functionality internally often outweighs licensing costs in both time and engineering effort
Authentication and access control across MCP gateway platforms
Enterprise authentication represents a critical differentiator separating production-ready platforms from basic implementations. The security fragmentation problem, where individual OAuth setups per server create multiple failure points, drives organizations toward centralized gateway solutions.
MintMCP authentication capabilities
MintMCP Gateway supports flexible authentication models:
- OAuth 2.0, SAML, SSO, and SCIM: Enterprise federation with identity providers and SCIM-driven RBAC
- Shared, per-user, and per-agent auth: Configure service accounts, enable individual OAuth flows, or govern agents with Agent Bundles and M2M auth
- SSO integration: Okta SAML SSO and Azure AD compatibility
- Automatic wrapping: OAuth protection applied to MCP endpoints without manual configuration
Industry-Standard authentication patterns
Leading platforms implement layered security approaches:
- Identity provider compatibility: Okta, Azure AD, Google Workspace integration
- Multi-factor authentication: Enforcement of MFA policies organization-wide
- Session management: Configurable timeouts and automatic token refresh
- Role-based access control: Team-based permissions for collaborative environments
Authorization models
Granular tool access control enables organizations to configure permissions by role, restricting write operations while enabling read-only access for specific teams. MintMCP extends this model through Virtual MCP Bundles, which create per-use-case endpoints with SCIM-driven membership, curated tools, and access policies for both human users and agent identities.
Monitoring, observability, and compliance reporting
Production MCP gateways must provide comprehensive visibility into agent behavior, tool usage, and security events. The "invisible agent" problem, where AI systems access tools without traditional visibility mechanisms, drives regulatory teams to demand complete audit trails.
MintMCP observability features
Real-time monitoring dashboards track:
- Tool call tracking: Every MCP invocation with complete context and user attribution
- Usage pattern analysis: Identify which tools teams use, detect security events, and measure performance
- Policy and governance visibility: Monitor tool-level allowlisting, rule-based policy outcomes, and agent activity across governed MCP endpoints
- Security alerts: Real-time notifications for policy violations and anomalous behavior
Compliance audit trails
Complete audit logs provide:
- SOC 2 Type II attestation support: Centralized logging for compliance reporting
- HIPAA Compliant (BAA Available) support: Audit trails and access controls for regulated healthcare workflows
- GDPR support: Audit trails and governed access controls for privacy-sensitive workflows
- Structured JSON logging: Integration with centralized telemetry and security workflows
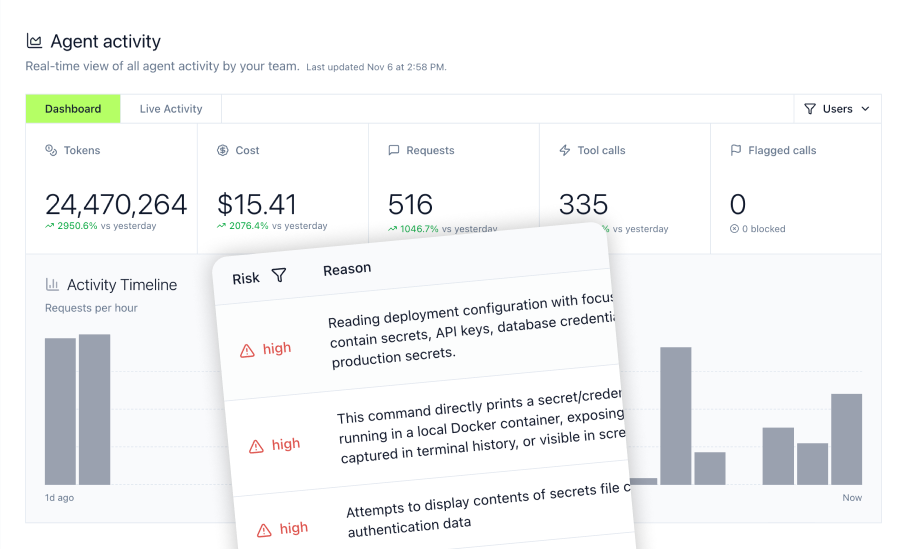
Agent Monitor for coding agent monitoring
MintMCP Agent Monitor provides specialized observability for coding agents:
- Track tool invocation and local activity: Monitor bash commands, file operations, prompt submissions, and MCP tool calls from Cursor and Claude Code
- MCP inventory visibility: See installed MCPs and monitor usage across teams
- Block risky operations: Prevent access to sensitive files, secrets, and dangerous command execution in real-time
- Complete command history: Audit trail of bash commands for security review
Organizations using coding agents require this specialized monitoring as agents operate with extensive system access, reading files, executing commands, and accessing production systems through MCP tools.
MCP server registry and connector ecosystem comparison
The breadth and quality of pre-built connectors significantly impact deployment speed and integration complexity. Organizations face integration chaos when forced to build custom connections for every data source.
MintMCP connector library
The centralized MCP registry provides installation for:
Database Connectors:
- PostgreSQL: Open-source relational database integration
- MySQL: Popular database with AI agent query capabilities
- MongoDB: NoSQL document database connector
- Redis: In-memory data structure store integration
- Snowflake: Cloud data warehouse with Cortex Analyst
- BigQuery: Google Cloud analytics platform
- Oracle, SQL Server, Cassandra: Enterprise database support
Search and Analytics:
- Elasticsearch: Enterprise search with semantic capabilities for AI-powered knowledge bases
Communication and Productivity:
- Gmail: Email automation with threading integrity
- Google Calendar: Schedule management integration
- Outlook and Outlook Calendar: Microsoft 365 connectivity
- Notion: Workspace documentation integration
- Linear: Issue tracking for development teams
Custom connector development
MintMCP supports custom connectors through three deployment models:
- Remote connectors: Point to existing HTTP-accessible MCP servers
- Hosted connectors: Deploy STDIO servers on MintMCP infrastructure with Docker image support
- Custom development: Build organization-specific integrations with full platform support
Competitor ecosystem comparison:
- Zapier: 8,000+ app integrations, but limited to workflow automation patterns
- Open-source platforms: Community-built servers with inconsistent security validation
- Enterprise platforms: Smaller curated registries focusing on core business systems
AI client compatibility: Claude ChatGPT Cursor and Multi-Platform support
Platform-agnostic AI client support eliminates the need for separate security implementations per agent while future-proofing infrastructure as the AI landscape evolves.
MintMCP client support
Universal compatibility spans:
- Claude Desktop and Claude Code: Anthropic's flagship AI assistants
- ChatGPT Custom GPTs: OpenAI integration with custom actions
- Cursor IDE: AI-powered code editor with Agent Monitor support
- Microsoft Copilot: Enterprise AI assistant integration
- Gemini: Google's AI platform connectivity
- Windsurf and Goose: Emerging coding assistants
- LibreChat and Open WebUI: Self-hosted AI interfaces
- Custom MCP clients: Flexible APIs supporting any protocol-compliant implementation
ChatGPT integration specifics
MCP Custom GPTs enable AI assistants to access internal tools through the MintMCP Gateway:
- Custom Actions: Connect ChatGPT to databases, Elasticsearch, and Snowflake
- OAuth authentication: Secure user-specific data access
- Tips for implementation: Best practices for reliable integrations
Coding agent monitoring
The MintMCP Agent Monitor specializes in monitoring coding agents operating with extensive system access:
- Cursor setup: Track tool calls and bash commands in real-time
- AWS Bedrock integration: Enterprise AI model monitoring
- Security rules: Block dangerous operations before execution
- Data retention policies: Configurable logging for compliance
Selection framework: Choosing the right MCP gateway for your enterprise
Evaluating MCP gateway platforms requires structured decision criteria balancing deployment speed, security compliance, and operational complexity.
Primary evaluation criteria
Deployment Speed Requirements:
- Managed SaaS-first platforms (MintMCP): Fast deployment with hosted connectors and pre-configured governance primitives
- Container-native solutions: Days to weeks, depending on Docker expertise
- Kubernetes platforms (TrueFoundry): Longer setup when teams need broader MLOps control plane capabilities
- Open-source implementations: Weeks to months for manual security setup
Security and Compliance Alignment:
- SOC 2 Type II attestation: Centralized controls and audit support for enterprise deployments
- HIPAA Compliant (BAA Available) support: Healthcare data handling requirements where required
- GDPR support: Governed access controls and audit trails for privacy-sensitive workflows
- Industry-specific needs: Finance, legal, healthcare, regulatory frameworks
Integration Ecosystem Breadth:
- Pre-built connectors: Database, Elasticsearch, Snowflake, productivity tools
- Custom development support: Hosted and custom connectors
- AI client compatibility: Claude, ChatGPT, Cursor, Gemini, Copilot support
Learning Curve and Training Investment:
- MintMCP: Purpose-built MCP governance with managed SaaS-first deployment
- Complex platforms: Longer competency ramps when teams must operate broader MLOps, API gateway, or container infrastructure
- Support resources: Quickstart guides, tutorials, professional services
Decision matrix by use case
Choose MintMCP When:
- Deploying MCP infrastructure and agent governance, not broader MLOps needs, in regulated industries
- Requiring rapid managed deployment rather than multi-week infrastructure projects
- Needing SOC 2 Type II attestation, HIPAA Compliant (BAA Available) support, or GDPR support without building audit infrastructure manually
- Supporting multiple AI clients, including Claude, ChatGPT, Cursor, Gemini, and Copilot, through a unified platform
- Prioritizing centralized authentication, SCIM-driven RBAC, credential management, audit logs, and rule-based policy
- Seeking purpose-built MCP focus rather than comprehensive MLOps platforms
Getting started
Organizations evaluating MCP gateway platforms should:
- Assess primary use case: MCP-focused vs. comprehensive MLOps requirements
- Identify compliance needs: SOC 2 Type II attestation, HIPAA Compliant (BAA Available) support, GDPR support, and other governance requirements
- Evaluate deployment timeline: Acceptable setup time from weeks to fast managed deployment
- Review AI client compatibility: Current and future agent platform needs
- Contact vendors: Request a MintMCP demo for custom requirements
Frequently asked questions
What is the difference between an MCP gateway and a network security gateway like unifi cloud gateway?
MCP gateways operate at the application layer as reverse proxies for AI agent-to-tool communication, while network security gateways like Unifi Cloud Gateway function at the network perimeter, controlling traffic flow. MCP gateways specifically manage Model Context Protocol connections between AI clients (Claude, ChatGPT, Cursor, Gemini, and Copilot) and MCP servers, providing tools and data access. Network gateways handle broader network security, VPN, firewall policies, and infrastructure connectivity.
Does MintMCP gateway support self-hosted deployment or only cloud-based?
MintMCP Gateway is managed SaaS-first with US and EU availability. VPC/self-hosted deployment is available on request for organizations requiring additional infrastructure control, data-sovereignty review, or strict regulatory deployment models.
How does OAuth authentication wrapping work for local stdio-based MCP servers?
MintMCP's OAuth brokering for stdio and hosted MCP servers helps transform local STDIO servers into governed services by hosting them on MintMCP infrastructure and wrapping MCP endpoints with enterprise authentication. The platform handles OAuth 2.0 flows, token management, and session handling, reducing the need for manual security implementation. Administrators can configure shared service accounts, enable individual OAuth flows, or govern agents through Agent Bundles with M2M auth.
What compliance certifications does MintMCP gateway hold for enterprise deployments?
MintMCP Gateway has SOC 2 Type II attestation and supports HIPAA Compliant (BAA Available) deployments. The platform provides audit logging of MCP interactions, access requests, and configuration changes. Organizations in regulated industries such as finance, healthcare, and legal can use built-in audit and governance workflows instead of building audit infrastructure manually with open-source alternatives.
What is the typical implementation timeline for deploying an MCP gateway in an enterprise?
Implementation timelines vary dramatically by platform. MintMCP Gateway supports fast managed deployment through managed SaaS-first infrastructure, hosted connectors, and pre-configured governance primitives. Kubernetes-based or broader MLOps platforms such as TrueFoundry can require longer setup depending on control-plane and cluster requirements. Open-source implementations can demand weeks to months for manual security setup, connector operations, and compliance infrastructure.