When evaluating Portkey alternatives for MCP gateway infrastructure, organizations face a critical choice between retrofitted API gateways and purpose-built MCP solutions. While traditional API gateways struggle with stateful session management and MCP-specific authorization requirements, MCP gateways natively understand JSON-RPC message structures and agent-specific security needs. This comprehensive guide examines the top five Portkey alternatives, with particular emphasis on why MintMCP is a strong choice for enterprise MCP deployment.
Key takeaways
- MintMCP stands out as a Portkey alternative for enterprise MCP infrastructure with SSO and SCIM-driven RBAC, tool-level allowlisting, and OAuth brokering for stdio and hosted MCP servers
- MCP gateways differ fundamentally from API gateways, requiring stateful session management, native JSON-RPC support, and MCP transport normalization across stdio, HTTP-streamable, and SSE deployments.
- The API management market grows from $6.85 billion in 2026 to $41.09 billion (estimates vary) by 2033, creating a significant opportunity for specialized MCP solutions
- Security gaps exist in traditional access controls for AI agent patterns, requiring MCP-specific authentication, fine-grained authorization, and continuous monitoring
- Organizations increasingly adopt federated multi-gateway approaches rather than single-vendor solutions, enabling MCP-focused platforms to complement existing API gateway investments
- Deployment speed separates leaders from laggards: MintMCP supports managed SaaS-first deployment for governed MCP access, with VPC and self-hosted options available on request
What is an MCP gateway and why organizations need one
MCP (Model Context Protocol) gateways function as centralized control planes to securely, reliably, and idiomatically connect AI agents to the growing ecosystem of MCP servers. Unlike traditional API gateways optimized for stateless REST interactions, MCP gateways natively understand JSON-RPC message structures, maintain stateful session mappings, and handle MCP-specific authorization, routing, and streaming patterns.
Core MCP gateway functions:
- Protocol translation from JSON-RPC to backend MCP server formats
- Session fan-out when clients send tool discovery requests
- Request routing based on tool names to correct backend servers
- Response multiplexing from multiple backends into a single streaming response
- State coordination with session IDs across backend connections
- Centralized authentication with OAuth 2.0, SSO, and federated identity providers
- Audit trail generation for every MCP interaction and tool invocation
Enterprise requirements driving MCP gateway adoption
The market opportunity is substantial: APIs account for 70-83% of internet traffic in 2025, and the API gateway segment is projected to dominate with 37.2% market share. Organizations moving from LLM experimentation to production AI agent deployments face critical challenges:
- Zero telemetry into AI tool usage and data access patterns
- No request history for security review or compliance audits
- Uncontrolled access to sensitive data and production systems
- Fragmented infrastructure requiring multiple platforms for hosting, gateway, and monitoring
- Inconsistent authentication across MCP servers and AI assistants
Traditional API gateways fail to address these challenges because MCP requires fundamentally different capabilities than stateless REST APIs.
1. MintMCP gateway: Enterprise MCP infrastructure platform
MintMCP Gateway transforms local and hosted MCP servers into production-ready services with managed deployment, OAuth protection, and enterprise monitoring. With SOC 2 Type II audited security controls, SSO and SCIM-driven RBAC, and tool-level access control, MintMCP helps close the security and governance gaps that plague traditional approaches.
Key MintMCP advantages:
- Managed stdio and hosted MCP deployment reduces containerization complexity and hosting overhead
- OAuth brokering for stdio and hosted MCP servers adds enterprise authentication to MCP servers
- SOC 2 Type II audited security controls with audit trails that support GDPR compliance programs
- Virtual MCP Bundles expose per-use-case endpoints with SCIM-driven membership and only the required tools
- Real-time monitoring dashboards for server health, usage patterns, and security alerts
- Granular tool access control by role, with tool-level allowlisting and rule-based policy
- Complete audit logs for every MCP interaction, access request, and configuration change
Security and governance features
MintMCP addresses the security gaps that traditional access controls fail to solve for dynamic agent-driven patterns. The platform provides:
- Shared and per-user authentication with flexibility for service accounts or individual OAuth flows
- SSO and SCIM-driven RBAC tied to IdP groups and Virtual MCP Bundle membership
- Centralized credential management for all MCP server API keys and tokens
- Rule-based policy enforcement for data access, usage controls, and tool-level authorization
- Hosted MCP connectors run by MintMCP with managed connector runtime, scaling, and isolation
- Gateway + Agent Monitor two-layer governance for MCP traffic, local bash commands, file operations, and coding-agent activity
Deployment speed and developer experience
While custom implementations can require weeks or months, MintMCP deploys governed MCP access quickly. The platform's approach enables:
- No changes to developer workflows, maintaining existing AI assistant integrations
- Self-service access where developers request and receive tool access through governed workflows
- Pre-configured policies for common use cases without slowing teams down
- Simple connection to MCP servers with automatic discovery and configuration
Integration ecosystem
MintMCP supports governance across major AI assistants, including Claude, Cursor, ChatGPT, Gemini, and Copilot. The platform integrates with critical enterprise systems through specialized MCP connectors:
- Elasticsearch MCP Server for AI-powered knowledge base search and log analysis
- Snowflake MCP Server for natural language queries against data warehouses
- Gmail MCP Server for AI-driven customer response automation
- Hosted MCP connectors run by MintMCP for enterprise systems and custom use cases
Pricing and support
MintMCP offers enterprise pricing with managed SaaS-first deployment in the US and EU, plus VPC and self-hosted options on request. Contact enterprise@mintmcp.com for detailed pricing and deployment options tailored to your organization's needs.
2. TrueFoundry MCP gateway
TrueFoundry positions itself as a comprehensive AI infrastructure platform with MCP gateway capabilities for teams seeking unified AI infrastructure. The platform combines model serving with gateway functionality for organizations that already operate ML and platform infrastructure.
TrueFoundry key capabilities:
- Low-latency gateway performance for latency-sensitive AI infrastructure
- Multi-region LLM gateway deployment with RBAC for model and MCP access
- Cost optimization features for cloud and model-serving infrastructure
- Self-hosted model support for running open models in-house
- Production reliability features for teams operating AI infrastructure at scale
Unified platform approach
TrueFoundry reduces context-switching by handling both model serving and gateway functions. For ML platform teams, this unified approach can simplify deployment workflows and centralize AI infrastructure operations.
Limitations to consider:
- Steeper learning curve compared to specialized MCP gateways
- Requires Kubernetes expertise for optimal deployment
- Best suited for organizations already invested in ML platform and Kubernetes operations
- Less emphasis on MintMCP-specific primitives such as Virtual MCP Bundles, Agent Bundles with M2M auth, hosted MCP connectors, and Gateway + Agent Monitor two-layer governance
3. IBM ContextForge
IBM ContextForge MCP Gateway brings IBM's enterprise integration patterns to the MCP ecosystem. The platform federates MCP and REST services for organizations with significant IBM infrastructure investments.
ContextForge strengths:
- Enterprise integration patterns for legacy system connectivity
- Hybrid cloud support across IBM Cloud and on-premises deployments
- Watson integration for AI-enhanced capabilities
- Compliance framework alignment with established IBM security standards
- Apache 2.0 licensing for open-source MCP gateway deployments
ContextForge limitations:
- Production readiness should be evaluated directly against current IBM ContextForge documentation and release status
- IBM ecosystem alignment may limit flexibility for multi-vendor strategies
- An enterprise licensing model typically involves complex pricing
- Less emphasis on MintMCP-specific primitives such as Virtual MCP Bundles, Agent Bundles with M2M auth, managed hosted MCP connectors, and Slack-native managed agents
For a detailed comparison, see MintMCP vs IBM ContextForge.
4. LiteLLM
LiteLLM functions as a lightweight proxy layer with multi-provider LLM routing and basic MCP gateway capabilities. The open-source foundation appeals to developer-first teams comfortable with self-hosted deployment.
LiteLLM core features:
- Multi-provider LLM routing with a unified API interface
- Cost tracking features for monitoring LLM spending
- Open-source foundation preventing vendor lock-in
- Self-hosted deployment for complete infrastructure control
- Rate-limiting capabilities for usage management
Developer experience
LiteLLM's developer-first approach provides flexibility for teams with strong technical expertise. The platform offers extensibility through code customization and integration with existing toolchains.
Significant drawbacks:
- Performance considerations: teams should benchmark LiteLLM against their own routing, streaming, and observability requirements
- Enterprise controls may require additional configuration or paid tiers for authentication, audit logging, and policy controls
- Documentation depth varies by feature and may require implementation work from engineering teams
- Rapid release cycles can increase production maintenance overhead
- Limited MCP-specific governance primitives compared with MintMCP capabilities such as SCIM-driven Virtual MCP Bundles, Agent Bundles, tool-update policy, and Gateway + Agent Monitor coverage
For a comprehensive comparison, review MintMCP vs LiteLLM.
5. Docker MCP gatewayn
Docker's MCP gateway positions as an open-source solution for orchestrating MCP servers from the Docker MCP Catalog. The platform provides centralized routing and policy enforcement with deployment via Docker Compose.
Docker MCP gateway benefits:
- OSS licensing with no vendor lock-in concerns
- Docker Compose deployment both locally and in production
- Centralized MCP server discovery from Docker catalog
- Simple policy enforcement for basic access control
- Container-native architecture for organizations standardized on Docker
Ideal use cases:
- Development and testing environments requiring a quick MCP server setup
- Organizations committed to the Docker ecosystem with existing container infrastructure
- Teams comfortable with OSS maintenance and self-support models
- Proof-of-concept projects before enterprise deployment
Production limitations:
- Managed enterprise identity workflows may require additional infrastructure for SSO, SCIM-driven RBAC, and OAuth brokering
- Built-in logs/traces; external monitoring is optional for advanced needs.
- Limited support options beyond community forums
- Manual scaling configuration versus managed SaaS-first deployment
- Connector runtime, scaling, and patching responsibility falls on the implementing organization
Evaluating MCP gateway security and compliance features
Security and compliance capabilities separate enterprise-ready MCP gateways from basic proxying solutions. Organizations must evaluate platforms against comprehensive requirements:
Essential security requirements:
- SOC 2 Type II attestation demonstrating continuous security controls
- Compliant with HIPAA standards, with BAA availability for healthcare data processing
- GDPR audit trail requirements, audit trails supporting GDPR compliance programs
- OAuth 2.0 and SSO flows for enterprise authentication
- SCIM-driven role-based access control with fine-grained permission models
- Tool-level allowlisting and rule-based policy for MCP-specific authorization
- Encryption at rest and in transit with industry-standard protocols
- Vulnerability scanning and regular security assessments
MintMCP security leadership
MintMCP Gateway is SOC 2 Type II audited, compliant with HIPAA standards, and provides complete audit trails for compliance programs. MintMCP signs BAAs. The platform enforces SSO, SCIM-driven RBAC, and tool-level access control for MCP servers, reducing security gaps in traditional approaches.
Authentication standards comparison
Traditional API gateways offer multiple authentication mechanisms but lack MCP-specific enhancements. MCP gateways must handle:
- Continuous authorization throughout stateful sessions versus one-time verification
- Agent-specific access patterns rather than human user workflows
- Tool-level permissions are not just API endpoint access
- Session state security across MCP transports and streaming responses
Traditional access controls can struggle in LLM deployments due to dynamic, agent-driven request patterns that differ fundamentally from predictable human API usage.
MCP server deployment and hosting options
Deployment models vary significantly across MCP gateway platforms, impacting operational complexity and time-to-production.
STDIO server deployment models
STDIO-based MCP servers present unique hosting challenges that purpose-built gateways solve:
- Local execution requires running servers on every developer machine
- Containerized hosting eliminates local installation but adds orchestration complexity
- Automatic lifecycle management ensures servers start, stop, and scale appropriately
- Environment variable handling securely manages credentials and configuration
- Dependency packaging resolves library conflicts and version requirements
MintMCP deployment advantages
MintMCP Gateway provides managed deployment for stdio-based and hosted MCP servers with built-in hosting and automatic lifecycle management. The platform eliminates infrastructure overhead that traditional approaches impose.
Managed hosting benefits
Organizations can reduce deployment time by using managed MCP gateway platforms versus self-hosted implementations. Benefits include:
- Fast deployment versus weeks of infrastructure setup
- Automatic scaling based on demand patterns
- Reduced maintenance overhead for server management
- Built-in monitoring without a separate observability stack
- Managed SaaS-first deployment in the US and EU, with VPC and self-hosted options available on request
High availability architecture
Enterprise MCP gateways provide production-grade reliability through:
- Automatic failover when primary servers become unavailable
- Load balancing across multiple backend instances
- Health checking with automatic removal of failed endpoints
- Redundancy eliminates single points of failure
- Disaster recovery with backup and restoration capabilities
Monitoring and observability for MCP gateways
Comprehensive observability differentiates enterprise MCP gateways from basic proxy solutions. Organizations require visibility into AI agent behavior that traditional monitoring tools cannot provide.
Essential monitoring metrics:
- Real-time usage dashboards showing active sessions and tool invocations
- Tool invocation tracking for every MCP tool call by the agent
- Latency metrics with p50, p95, and p99 percentile tracking
- Error rate monitoring with detailed failure analysis
- Cost analytics per team and project for chargeback
- Data access logging showing exactly what data each AI accesses
- Anomaly detection for unusual agent behavior patterns
- Performance SLA tracking against defined service levels
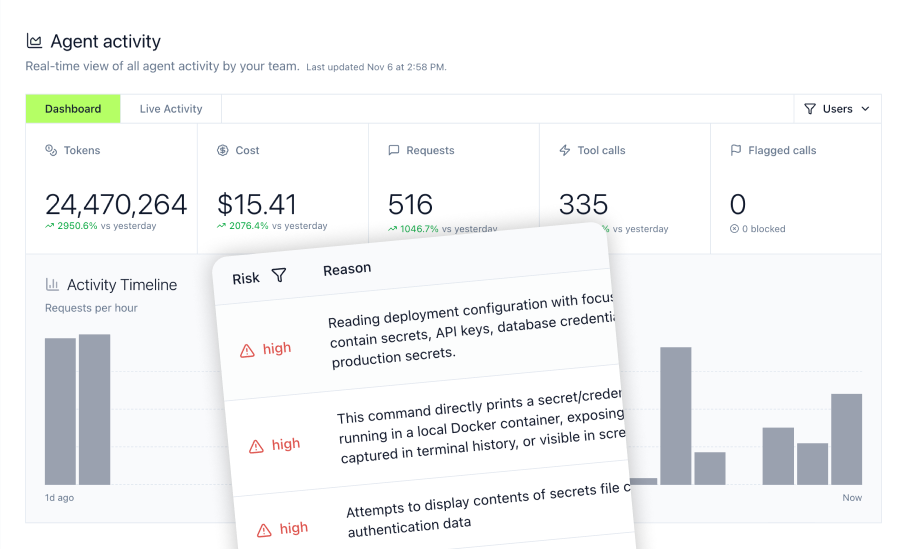
MintMCP observability platform
MintMCP Gateway provides real-time monitoring dashboards for server health, usage patterns, and security alerts with complete visibility into every MCP interaction. The platform tracks:
- Every tool call with request/response logging where configured
- Security events, including authentication failures and policy violations
- Performance metrics across MCP servers and AI assistants
- Usage analytics for capacity planning and optimization
LLM proxy for coding agent monitoring
MintMCP LLM Proxy monitors MCP tool invocations, bash commands, and file operations from coding agents like Cursor and Claude Code. The platform provides:
- Complete MCP inventory showing which MCPs are installed across teams
- Sensitive file protection preventing access to .env files, SSH keys, and credentials
- Command history with a complete audit trail for security review
- Risky operation blocking in real-time before execution
Security event monitoring
Zero-trust security models for AI workloads require continuous monitoring beyond traditional authentication. MCP gateways must track:
- Agent authentication events with success/failure patterns
- Tool access attempts, including denied requests
- Data exfiltration indicators from unusual access patterns
- Policy violations with automated alerting and response
Choosing the right MCP gateway for your organization
Selecting the optimal MCP gateway platform requires evaluating technical capabilities, organizational requirements, and long-term strategic fit.
Decision framework for MCP gateway selection
Organizations should assess platforms across six dimensions:
- MCP protocol native support: Does the gateway understand JSON-RPC, maintain stateful sessions, and handle MCP transports without custom development?
- **Security and compliance: **Is the platform SOC 2 Type II audited, with SSO, SCIM-driven RBAC, and complete audit trails required for your industry?
- Deployment speed: Can you deploy governed MCP access quickly versus weeks or months for production readiness?
- Enterprise support: Does the vendor offer SLAs, dedicated support, and assistance with implementation?
- Performance at scale: What latency overhead does the gateway add, and how does it handle production traffic volumes?
- Total cost of ownership: What are the direct costs plus operational overhead for maintenance and management?
Cost-Benefit analysis factors
The large enterprises segment, expected to lead with an estimated 65% market share in 2025, demonstrates significant enterprise investment in API infrastructure. When evaluating MCP gateways:
- Build versus buy decision: Self-built solutions require months of development versus faster deployment with commercial platforms
- Operational overhead: Self-hosted gateways impose an ongoing DevOps burden versus managed services
- Security assurance costs: Building comparable controls independently can add significant security and audit overhead
- Opportunity costs: Engineering time spent on gateway infrastructure versus product features
- Risk mitigation: Production outages from immature self-built solutions versus enterprise SLAs
Implementation timeline expectations:
- MintMCP Gateway: Deploy governed MCP access quickly with pre-configured policies and no workflow changes
- Commercial MCP gateways: Days to weeks for implementation with vendor support
- Traditional API gateways: Weeks to months for MCP functionality development
- Self-hosted open-source: Months for production-ready deployment with full features
MintMCP selection advantages
MintMCP Gateway reduces the build versus buy burden by providing enterprise MCP infrastructure with managed deployment. The platform offers:
- **SOC 2 Type II audited **security controls and compliance with HIPAA standards, with BAA availability for compliance programs
- Pre-configured policies for common use cases without security gaps
- No vendor lock-in through standard MCP protocol support
- Transparent pricing with enterprise SLAs and dedicated support
- Production-ready governance primitives including Virtual MCP Bundles, Agent Bundles, tool-update policy, and Gateway + Agent Monitor coverage
Frequently asked questions
What is the difference between an MCP gateway and a traditional API gateway?
MCP gateways differ from traditional API gateways in protocol and state. REST gateways handle stateless HTTP; MCP gateways natively parse JSON-RPC, maintain stateful sessions, and coordinate session IDs across backends. MCP deployments commonly use stdio for local servers and streamable HTTP or SSE for remote and hosted deployments.
How do I deploy stdio-based MCP servers with a gateway?
STDIO-based MCP servers traditionally run locally on developer machines, creating deployment and security challenges. MintMCP Gateway provides managed deployment that hosts stdio servers, adds OAuth protection, and transforms local servers into production services with monitoring and audit logs. Alternative approaches require manual containerization, orchestration configuration, environment variable management, and custom deployment scripting.
Which MCP gateway alternatives support SOC 2 compliance?
SOC 2 Type II audited security controls are important for enterprise deployments. MintMCP Gateway is SOC 2 Type II audited and includes audit trails that support compliance programs. Portkey and Composio also hold SOC 2 Type II, so buyers should treat SOC 2 Type II as a baseline requirement and compare MCP-specific controls such as SCIM-driven RBAC, Virtual MCP Bundles, Agent Bundles, and tool-level policy.
Can I use AWS API gateway or Azure APIM for MCP server management?
While technically possible, using AWS API Gateway or Azure API Management for MCP server infrastructure requires extensive custom development. These platforms lack native JSON-RPC understanding, stateful session management, and MCP-specific tool authorization that MCP gateways provide automatically.